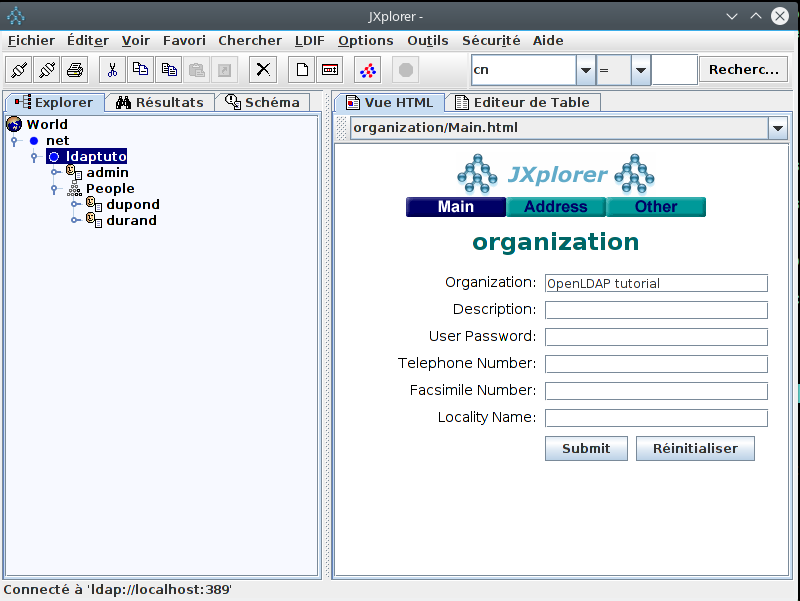
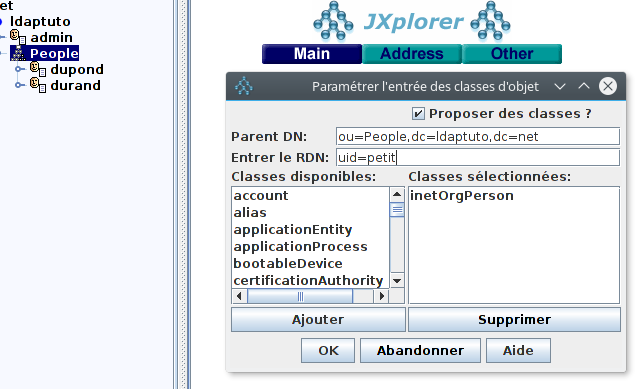
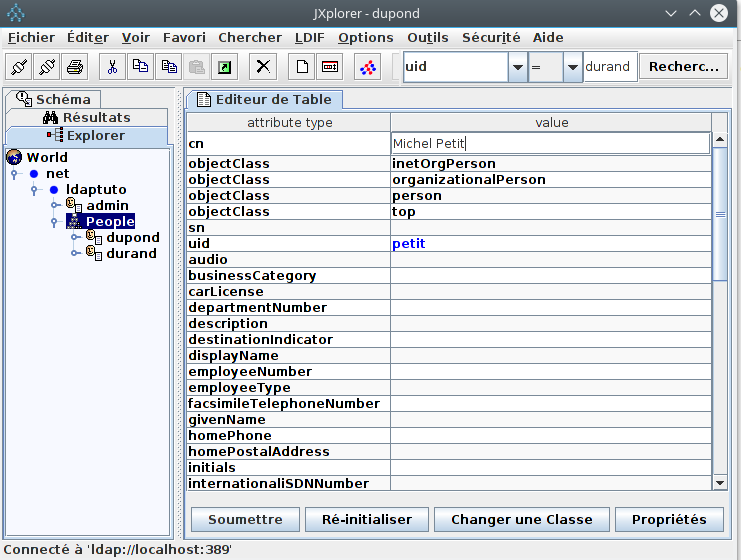
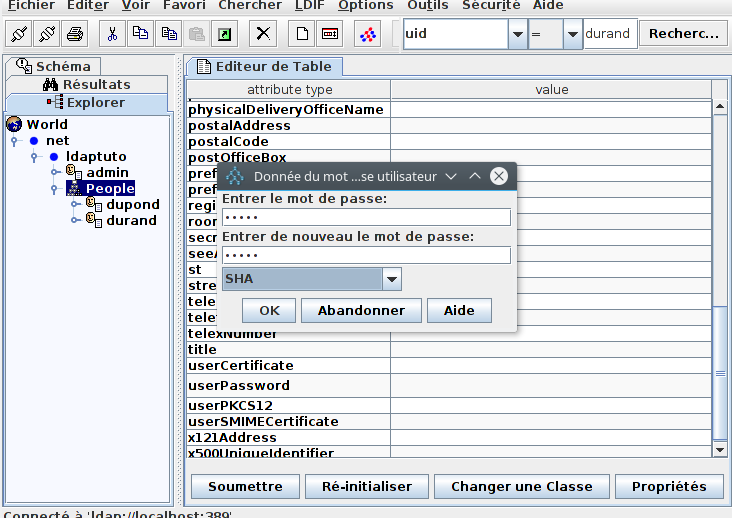
« OpenLDAP password policy » is an overlay that allows you to set up an efficient management of the authentication accounts of people referenced in the OpenLDAP directory. This management concerns in particular the passwords of these persons. This article will show how to configure the OpenLDAP server to activate the« password policy » overlay and implement this management. Prerequisite: The article Adding data to the directory and its prerequisites are read. The OpenLDAP server is installed and the data of the article are entered.
1. Enable ppolicy schema (OpenLDAP password policy)
By default, the ppolicy schema is installed: /etc/ldap/schema/ppolicy.ldif, but not enabled. To enable it:ldapmodify -x -a -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -f /etc/ldap/schema/ppolicy.ldifTo check the schema loading :
ldapsearch -x -s one -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -b cn=schema,cn=config cn -LLL
dn: cn={0}core,cn=schema,cn=config
cn: {0}core
dn: cn={1}cosine,cn=schema,cn=config
cn: {1}cosine
dn: cn={2}nis,cn=schema,cn=config
cn: {2}nis
dn: cn={3}inetorgperson,cn=schema,cn=config
cn: {3}inetorgperson
dn: cn={4}ppolicy,cn=schema,cn=config
cn: {4}ppolicy
Notice the presence of the ppolicy schema in addition to the four schemas that are enabled by default.
2. Enable the ppolicy overlay
Create the LDIF command file: ppolicy-module.ldifvi ppolicy-module.ldifEnter in the editor and save:
dn: cn=module{0},cn=config
changeType: modify
add: olcModuleLoad
olcModuleLoad: ppolicy
Execute the modify command contained in the file:
ldapmodify -x -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -f ppolicy-module.ldifTo check the module activation:
ldapsearch -x -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -b cn=config "(objectClass=olcModuleList)" olcModuleLoad -LLL
dn: cn=module{0},cn=config
olcModuleLoad: {0}back_mdb
olcModuleLoad: {1}ppolicy
Notice the presence of the ppolicy module in the list, while default only back_mdb (database management module) is enabled.
3. Configuring the ppolicy overlay
Create the LDIF command file: ppolicy-conf.ldifvi ppolicy-conf.ldifEnter in the editor and save:
dn: olcOverlay=ppolicy,olcDatabase={1}hdb,cn=config
objectClass: olcPpolicyConfig
olcOverlay: ppolicy
olcPPolicyDefault: cn=ppolicy,dc=ldaptuto,dc=net
olcPPolicyUseLockout: FALSE
olcPPolicyHashCleartext: TRUE
Add the entry contained in the file:
ldapmodify -x -a -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -f ppolicy-conf.ldifTo verify that the configuration is actually enabled:
ldapsearch -x -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -b cn=config "(objectClass=olcPpolicyConfig)" -LLL
dn: olcOverlay={0}ppolicy,olcDatabase={1}hdb,cn=config
objectClass: olcPPolicyConfig
olcOverlay: {0}ppolicy
olcPPolicyDefault: cn=ppolicy,dc=ldaptuto,dc=net
olcPPolicyHashCleartext: TRUE
olcPPolicyUseLockout: FALSE
Three configuration settings:
- olcPPolicyDefault: Specifies a configuration DN used by default (see next paragraph).
- olcPPolicyHashCleartext: Indicates whether passwords should be encrypted systematically. Advise: This setting should be TRUE.
- olcPPolicyUseLockout: Indicates whether the error message returned when attempting to connect to a locked account is a message specific to that locked state (TRUE), or a general failed login message (FALSE). FALSE is more secure (no indication to a possible pirate), TRUE is more convenient.
4. Configure a password policy
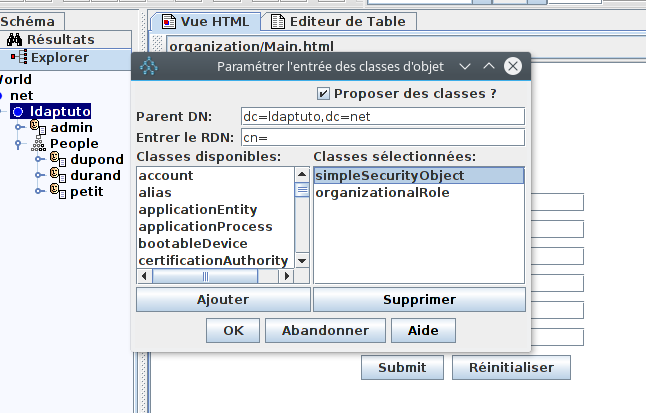
We will configure the entry specified in the olcPPolicyDefault parameter of the ppolicy overlay configuration, i.e. cn=ppolicy,dc=ldaptuto,dc=net. To do this we will create an LDIF file that will allow to add this entry.vi ppolicy-defaut.ldifEnter in the editor and save:
dn: cn=ppolicy,dc=ldaptuto,dc=net objectClass: device objectClass: pwdPolicyChecker objectClass: pwdPolicy cn: ppolicy pwdAllowUserChange: TRUE pwdAttribute: userPassword pwdCheckQuality: 1 pwdExpireWarning: 600 pwdFailureCountInterval: 30 pwdGraceAuthNLimit: 5 pwdInHistory: 5 pwdLockout: TRUE pwdLockoutDuration: 0 pwdMaxAge: 0 pwdMaxFailure: 5 pwdMinAge: 0 pwdMinLength: 5 pwdMustChange: FALSE pwdSafeModify: FALSEAdd the entry contained in the file:
ldapmodify -x -a -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -f ppolicy-defaut.ldifTo verify the result:
ldapsearch -x -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -b dc=ldaptuto,dc=net "(objectClass=pwdPolicy)" -LLL16 Settings (all listed attributes) allow you to set up an efficient and effective policy for passwords and user account management. The following command gives you full details about these parameters:
man slapo-ppolicyFor example, pwdMinLength has been set to 5, which means that a password can not be less than 5 characters in length. Let’s test:
ldappasswd -x -H ldap://localhost -D uid=durand,ou=people,dc=ldaptuto,dc=net -w durand -s dura Result: Constraint violation (19) Additional info: Password fails quality checking policyThis command allows Alain Durand to log in with his username and password (-D uid=durand,ou=people,dc=ldaptuto,dc=net and -w durand) and change this password with the new value provided (-s dura). The command fails because the new password has only 4 characters.
ldappasswd -x -H ldap://localhost -D uid=durand,ou=people,dc=ldaptuto,dc=net -w durand -s duranThe command succeeds because the new password has 5 characters. To verify the password modification:
ldapsearch -x -H ldap://localhost -D uid=durand,ou=people,dc=ldaptuto,dc=net -w durand -b dc=ldaptuto,dc=net ldap_bind: Invalid credentials (49)The old password is not accepted and the same command with the new password: duran, should succeed. Another setting: pwdCheckModule controls the quality of the contents of passwords. This setting specifies the file name of a native shared library that ensures this function. Before informing it, it will first be necessary to ensure that this library is present. pqChecker is a library that can be used to control passwords content strength for ppolicy overlay. To use it, you should modify the default password policy setting.
vi modifpp.ldifEnter in the editor and save:
dn: cn=ppolicy,dc=ldaptuto,dc=net changeType: modify add: pwdCheckModule pwdCheckModule: pqchecker.soExecute the modify command contained in the file:
ldapmodify -x -a -H ldap://localhost -D cn=admin,dc=ldaptuto,dc=net -w admin -f modifpp.ldifpqchecker.so is the quality control library for the contents of passwords. By default it is installed at /usr/lib/ldap. It requires by default a password with at least 1 uppercase, 1 lowercase, 1 digit and 1 special character (not alphabetic). Further details about it may be read on http://www.meddeb.net/pqchecker]]>